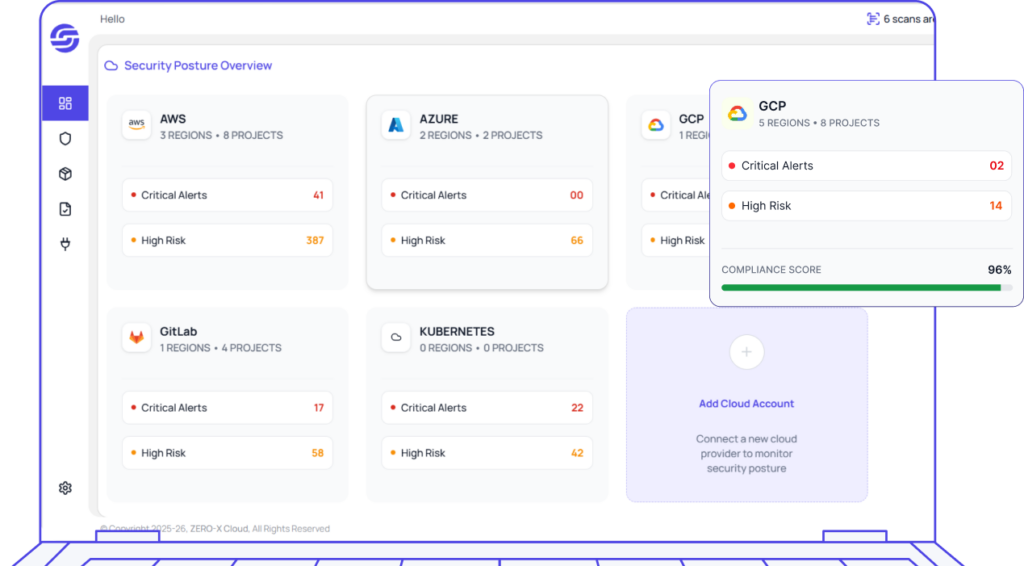
85%
Faster Risk Detection
By continuously scanning configurations, assets, and activity in real time.
Zero-X instantly identifies misconfigurations, exposed services, and vulnerabilities across cloud environments before they escalate into critical risks.
From Risk Detection

to Instant Remediation

Cloud Misconfiguration Detection
Continuously detect risky cloud misconfigurations across AWS and GCP— flagging open access, public storage, and weak encryption, aligned with CIS benchmarks.
Identity & Access Management (CIEM)
Eliminate excessive permissions and enforce least-privilege across users and roles.
Public Exposure & Attack Surface
Discover internet-exposed assets in real time and isolate unsafe resources faster.
Continuous Monitoring & Risk Scoring
Prioritize issues by business context, impact, and sensitivity for faster remediation.
Compliance Mapping & Guardrails
Map risks to frameworks and enforce guardrails with policy-as-code.
Cloud Security Vulnerabilities
Categorize weaknesses by severity so teams can fix the highest-risk issues first.






From Alert to Fix —
Instantly
No tickets. No delays. Just resolved risks.
Beyond code we detect, fix and secure your applications end-to-end.
Beyond code
to Instant Remediation
your applications end-to-end.
01
Misconfigurations
-
 Flags risky defaults—open SGs, weak encryption, and public buckets.
Flags risky defaults—open SGs, weak encryption, and public buckets. -
 Maps findings to CIS benchmarks and best practices.
Maps findings to CIS benchmarks and best practices. -
 Prioritized by blast radius,asset sensitivity, and tags.
Prioritized by blast radius,asset sensitivity, and tags.
02
Excessive Permissions (CIEM)
-
 Auto-generate least-privilege policies with review/approve flow
Auto-generate least-privilege policies with review/approve flow -
 Right-size access by account, role, and service
Right-size access by account, role, and service -
 Full audit trail with SLAs and ticketing
Full audit trail with SLAs and ticketing
03
Public Exposure & Exploitability
-
 Finds internet-exposed resources and reachable paths
Finds internet-exposed resources and reachable paths -
 Correlates CVEs/misconfigs with network exposure for real risk
Correlates CVEs/misconfigs with network exposure for real risk -
 One-click quarantine/auto-remediation via cloud APIs
One-click quarantine/auto-remediation via cloud APIs
04
Cloud Security Vulnerabilities
-
 Security gaps in cloud resources
Security gaps in cloud resources -
 Risk of data access or service disruption
Risk of data access or service disruption -
 Severity-based prioritization for quick fixes
Severity-based prioritization for quick fixes
“Zero-X is built to meet global security and compliance standards.”
Plans & Pricing
Choose a plan that fits your workflow. Scale effortlessly with flexible pricing designed for every stage of growth.

Developer Plan
For small projects and exploration.
Free
- 1 User account
- 2 Data Source
- Upto 500 Resources
- Upto 5 Daily Scans

Pro Plan
For teams in growing businesses
Billed Annually or Monthly
- 5 User account
- 10 Data Sources
- Upto 1000 Resources
- Upto 50 Daily Scans

Enterprise Plan
For teams in enterprises with complex needs
Billed Annually
- Multiple users
- Unlimited Data Sources
- Multiple Resources
- Unlimited Scans
- SAML/SSO Integration
Got Questions?
We’ve Got Answers.
Find quick answers or contact our support team.